If you use splunk, you probably use lookups to add handy data to your searches and alerts.
If you use lookups, you have probably run into a situation where you’ve wanted to update a lookup file.
If you’ve wanted to…Okay I’m done with that. Similarly, you’ve probably found the process of googling how to update your csv frustrating as well. Most of the results assume you want to create a process to automatically update a lookup via a saved search. That’s a great idea, and here are some great examples.
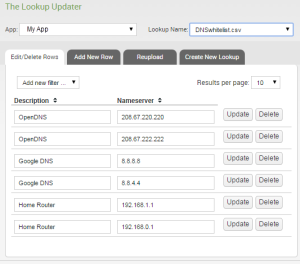
But what if I have a simple csv of a few values and I want to update it once? Say I have a CSV with whitelisted DNS servers. I use it to filter out DNS traffic to known-good servers in the search I use to detect rogue traffic.
| Description | Nameserver |
|---|---|
| OpenDNS | 208.67.220.220 |
| OpenDNS | 208.67.222.222 |
| Google DNS | 8.8.8.8 |
| Google DNS | 8.8.4.4 |
So I don’t want to automatically update this thing, I just want to add a row for my home router (whoops!).
How in the hell can I add it? I started looking at Splunk’s documentation and searching around Splunk’s stack-exchange Q&A site. I was preparing some sort of hairy query to combine inputlookup, something to create records out of thin air, and then deduping the results and outputlookup to put it back into the table.
That sucks, especially for a one-off. Okay, so instead, how about I just download the csv file, edit it on my PC, then reupload it? Sounds cumbersome.
Thing is, I didn’t need to think that hard.
We have the Sideview Utils installed. Included is a tool called, handily enough, The Lookup Updater. It lets me just edit the file in the web interface.
Go to the Sideview Utils app within Splunk. In the menu find Tools, then The Lookup Updater. From here you can edit your lookups to your heart’s content.
That’s all I needed to do. Here’s all there is to it: